
In 2025, the O-RAN ALLIANCE Security Work Group (WG11) achieved major accomplishments that further strengthened the O-RAN security posture.
As O-RAN continues to gain real world deployment experience, WG11 will continue strengthening the security posture with a continuing focus on the Operator Priorities in 2026.
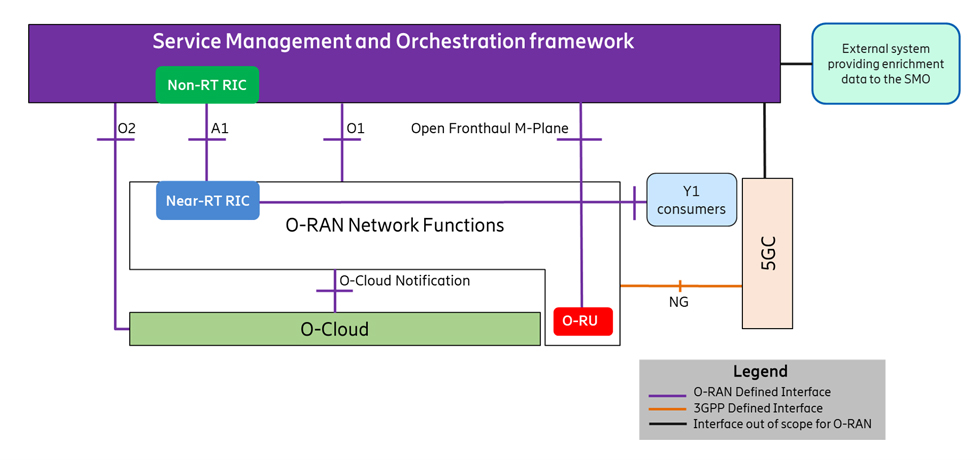
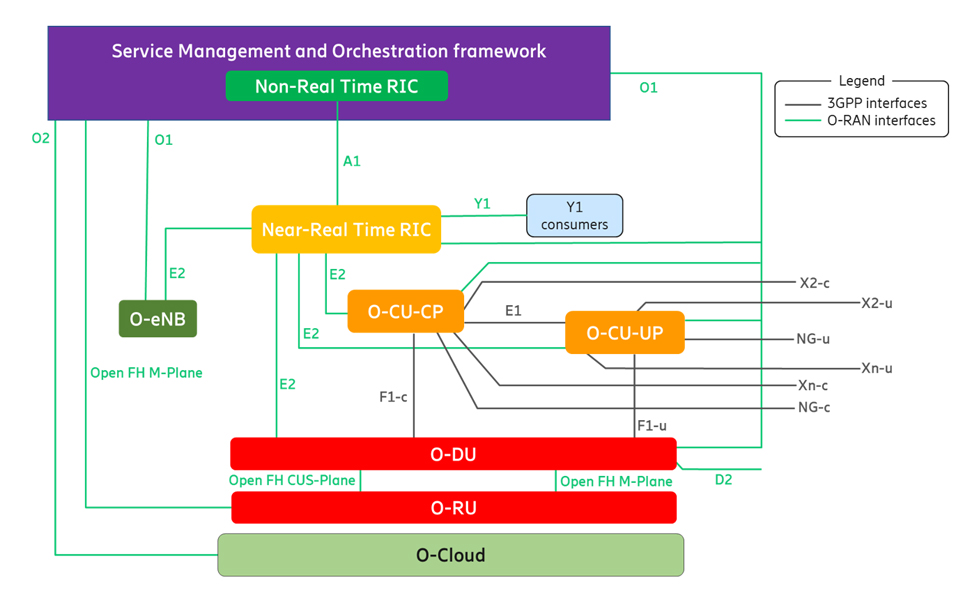
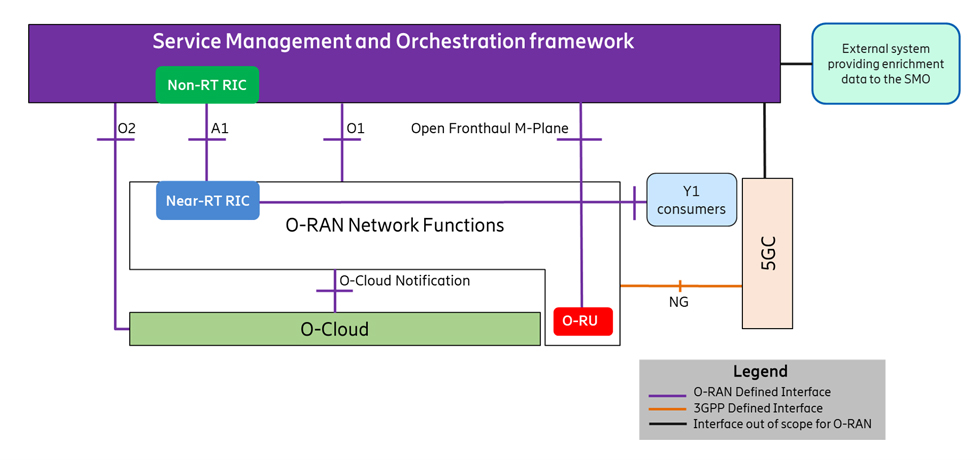
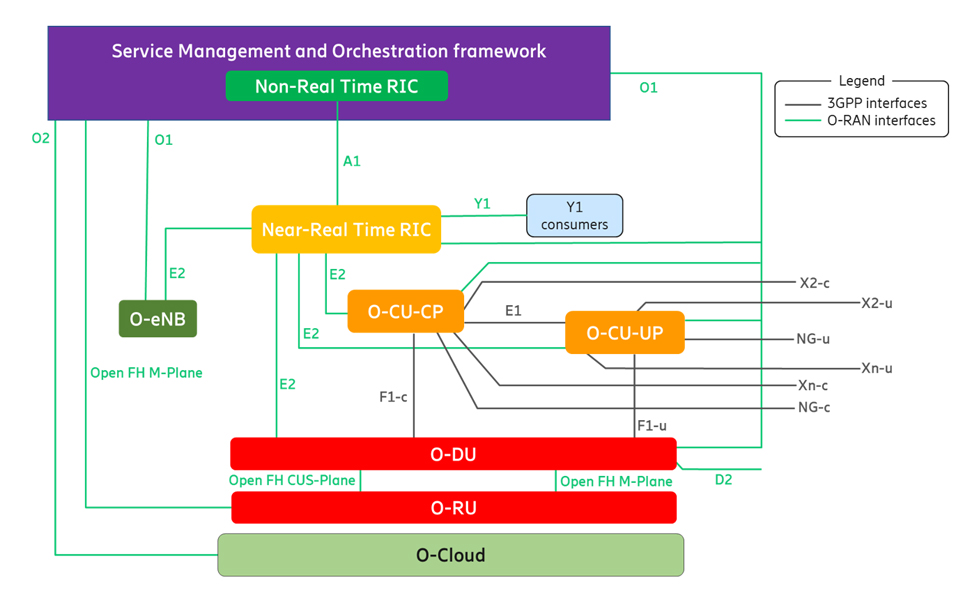
WG11 provides security requirements across the O-RAN architecture, including architecture elements and interfaces, as shown in Figures 1 and 2. 2025 marked a major milestone for the O-RAN ALLIANCE with the European Telecommunications Standards Institute (ETSI) and the Alliance for Telecommunications Industry Solutions (ATIS) publication of its four primary security documents: O-RAN Security Requirements and Controls Specifications [1], O-RAN Security Protocols Specification [2], O-RAN Security Test Specifications [3], and O-RAN Threat Management and Risk Assessment Technical Report [4]. Additionally, the Telecommunications Technology Association (TTA) signed a cooperation agreement to adopt the O-RAN standards. ETSI, ATIS and TTA publication is an acknowledgement of the maturity of the O-RAN ALLIANCE security specifications by standards development organizations (SDOs).
In early 2025, the O-RAN ALLIANCE polled its operator members for their deployment priorities and WG11 used the security-related priorities to guide its 2025 work. The Operator Priorities indicate their shift from evaluating the O-RAN architecture to deploying O-RAN networks.
The Operator Priorities for security address requirements for real-world implementation of O-RAN network deployments. The security priorities are:
These priorities highlight the practical challenges facing operators as they move to O-RAN.
WG11 responded to the call to action by partnering with the O-RAN Open Fronthaul work group (WG4) on Open Fronthaul security the O-Cloud work group (WG6) on O-Cloud security specifications and tests, and the O-RAN Testing Integration Focus Group (TIFG) on security assurance. WG11 also completed studies on certificate management, applied a zero trust framework to fill security gaps, and advanced the O-Cloud security architecture. The specified security requirements and controls have achieved a high-level security posture based upon a ZTA, as shown in Tables 1 and 2. Further details about these security requirements can be found in [1].
Table 1: O-RAN Interface Security
Cross-platform or transversal requirements apply to all O-RAN architecture elements and interfaces. Table 2 lists the mandatory O-RAN requirements for each category of transversal requirements, with details provided in [1].
Table 2: O-RAN Cross-Platform Security Requirements
Operators want security tests that can be used by third party testers to certify that a vendor provided O-RAN element, such as an O-RU, meets the O-RAN security requirements and controls defined in [1]. In addition to defining and refining tests for the security controls, WG11 has partnered with the O-RAN Test and Integration Focus Group (TIFG) and Global System for Mobile Communications Association (GSMA) to define security assurance specifications (SCAS) that ensure each O-RAN architecture element is securely implemented according to its specifications. SCAS documents will be publicly available in 2026.
The O-RAN ALLIANCE has publicly committed to pursue a Zero Trust Architecture in accordance with the US National Institute of Standards and Technology (NIST) SP 800-207 [6]. The NIST seven tenets of zero trust include per session dynamic access control based on least privilege, data and resource protection, and monitoring of all resources. In 2024, WG11 began its zero trust analysis of the O-RAN security specifications and controls to identify gaps in the specifications in order to meet Initial stage of maturity level defined in the US Department of Homeland Security Cybersecurity Infrastructure Security Agency (CISA) zero trust maturity model (ZTMM) [7]. The gap analysis uses the Identity, Data, Networks, Applications and Workloads, and Devices pillars of the ZTMM. In 2025, WG11 filled gaps in the O-RAN security specifications by enhancing requirements for least privilege access control, pre-configured expiration time on authorization decisions, data and model protection, and application package protections. WG11 also analysed the ZTMM Cross-cutting Capabilities (visibility and analytics, automation and orchestration, and governance) to determine which are in scope for O-RAN definition. Still requiring additional specifications are backup capabilities, network segmentation policies and monitoring, supply chain protections, defining asset data needed for operator inventories, and O-Cloud hardware accelerator abstraction layer (AAL) protections.
Additionally, O-RAN ALLIANCE WG11 held its 2nd annual ZTA Standardization Workshop, a forum for key stakeholders, including 3GPP members, to advance zero trust architecture (ZTA) in communications critical infrastructure. The outcomes of the meeting, listed below, will lead to strong security standards built into 5G, 5G Advanced, and 6G.
WG11 has active work items for ZTA, Secure AI, Continuous Security Monitoring, and PQC that will provide the foundation for secure O-RAN in 6G.
The O-Cloud is a foundational architecture element of O-RAN because it enables the disaggregation of O-RAN software and hardware, giving operators the ability to use commercially available hardware in the RAN. Through security analysis, the O-Cloud security requirements and controls were enhanced in the areas of security logging, software integrity, certificate and key management, accelerator abstraction layer, admission controllers, and container and VM isolation. These requirements and controls are complemented by security test specifications that define how to verify implementation and support consistent assessment.
Traditional RAN deployments are single vendor solutions, with all components of the eNodeB or gNodeB as well as the network manager provided by the same vendor. The gNodeB purpose-build elements are delivered with pre-installed vendor certificates signed by the vendor’s root of trust. Certificate management, including the certificate authority (CA) is typically handled by the network manager. The open interfaces in the O-RAN architecture enables a multi-vendor network with communication and management over standardized, open interfaces. To support certificate management, O-RAN has defined requirements using CMPv2 [6] covering the following use cases:
In 2026 WG11 will work with WG2, WG3, WG4, WG5, WG6 and WG10 to refine certificate management implementation details for each of these use cases.
Operator priorities will continue driving WG 11. Key 2026 initiatives in WG11 are to
[1] O-RAN Security Requirements and Controls Specifications, version 14.0, O-RAN ALLIANCE, February 2026.
[2] O-RAN Security Protocols Specifications, version 14.0, O-RAN ALLIANCE, February 2026.
[3] O-RAN Security Tests Specifications, version 12.0, O-RAN ALLIANCE, February 2026.
[4] O-RAN Security Threat Modeling and Risk Assessment, version 8.0, O-RAN ALLIANCE, February 2026.
[5] O-RAN Architecture Description, version 16, O-RAN ALLIANCE, February 2026.
[6] NIST Special Publication 800-207, "Zero Trust Architecture", August 2020, https://doi.org/10.6028/NIST.SP.800-207
[7] Zero Trust Maturity Model (ZTMM), version 2.0, US DHS CISA, April 2023.

In 2025, the O-RAN ALLIANCE Security Work Group (WG11) achieved major accomplishments that further strengthened the O-RAN security posture.
As O-RAN continues to gain real world deployment experience, WG11 will continue strengthening the security posture with a continuing focus on the Operator Priorities in 2026.
WG11 provides security requirements across the O-RAN architecture, including architecture elements and interfaces, as shown in Figures 1 and 2. 2025 marked a major milestone for the O-RAN ALLIANCE with the European Telecommunications Standards Institute (ETSI) and the Alliance for Telecommunications Industry Solutions (ATIS) publication of its four primary security documents: O-RAN Security Requirements and Controls Specifications [1], O-RAN Security Protocols Specification [2], O-RAN Security Test Specifications [3], and O-RAN Threat Management and Risk Assessment Technical Report [4]. Additionally, the Telecommunications Technology Association (TTA) signed a cooperation agreement to adopt the O-RAN standards. ETSI, ATIS and TTA publication is an acknowledgement of the maturity of the O-RAN ALLIANCE security specifications by standards development organizations (SDOs).
In early 2025, the O-RAN ALLIANCE polled its operator members for their deployment priorities and WG11 used the security-related priorities to guide its 2025 work. The Operator Priorities indicate their shift from evaluating the O-RAN architecture to deploying O-RAN networks.
The Operator Priorities for security address requirements for real-world implementation of O-RAN network deployments. The security priorities are:
These priorities highlight the practical challenges facing operators as they move to O-RAN.
WG11 responded to the call to action by partnering with the O-RAN Open Fronthaul work group (WG4) on Open Fronthaul security the O-Cloud work group (WG6) on O-Cloud security specifications and tests, and the O-RAN Testing Integration Focus Group (TIFG) on security assurance. WG11 also completed studies on certificate management, applied a zero trust framework to fill security gaps, and advanced the O-Cloud security architecture. The specified security requirements and controls have achieved a high-level security posture based upon a ZTA, as shown in Tables 1 and 2. Further details about these security requirements can be found in [1].
Table 1: O-RAN Interface Security
Cross-platform or transversal requirements apply to all O-RAN architecture elements and interfaces. Table 2 lists the mandatory O-RAN requirements for each category of transversal requirements, with details provided in [1].
Table 2: O-RAN Cross-Platform Security Requirements
Operators want security tests that can be used by third party testers to certify that a vendor provided O-RAN element, such as an O-RU, meets the O-RAN security requirements and controls defined in [1]. In addition to defining and refining tests for the security controls, WG11 has partnered with the O-RAN Test and Integration Focus Group (TIFG) and Global System for Mobile Communications Association (GSMA) to define security assurance specifications (SCAS) that ensure each O-RAN architecture element is securely implemented according to its specifications. SCAS documents will be publicly available in 2026.
The O-RAN ALLIANCE has publicly committed to pursue a Zero Trust Architecture in accordance with the US National Institute of Standards and Technology (NIST) SP 800-207 [6]. The NIST seven tenets of zero trust include per session dynamic access control based on least privilege, data and resource protection, and monitoring of all resources. In 2024, WG11 began its zero trust analysis of the O-RAN security specifications and controls to identify gaps in the specifications in order to meet Initial stage of maturity level defined in the US Department of Homeland Security Cybersecurity Infrastructure Security Agency (CISA) zero trust maturity model (ZTMM) [7]. The gap analysis uses the Identity, Data, Networks, Applications and Workloads, and Devices pillars of the ZTMM. In 2025, WG11 filled gaps in the O-RAN security specifications by enhancing requirements for least privilege access control, pre-configured expiration time on authorization decisions, data and model protection, and application package protections. WG11 also analysed the ZTMM Cross-cutting Capabilities (visibility and analytics, automation and orchestration, and governance) to determine which are in scope for O-RAN definition. Still requiring additional specifications are backup capabilities, network segmentation policies and monitoring, supply chain protections, defining asset data needed for operator inventories, and O-Cloud hardware accelerator abstraction layer (AAL) protections.
Additionally, O-RAN ALLIANCE WG11 held its 2nd annual ZTA Standardization Workshop, a forum for key stakeholders, including 3GPP members, to advance zero trust architecture (ZTA) in communications critical infrastructure. The outcomes of the meeting, listed below, will lead to strong security standards built into 5G, 5G Advanced, and 6G.
WG11 has active work items for ZTA, Secure AI, Continuous Security Monitoring, and PQC that will provide the foundation for secure O-RAN in 6G.
The O-Cloud is a foundational architecture element of O-RAN because it enables the disaggregation of O-RAN software and hardware, giving operators the ability to use commercially available hardware in the RAN. Through security analysis, the O-Cloud security requirements and controls were enhanced in the areas of security logging, software integrity, certificate and key management, accelerator abstraction layer, admission controllers, and container and VM isolation. These requirements and controls are complemented by security test specifications that define how to verify implementation and support consistent assessment.
Traditional RAN deployments are single vendor solutions, with all components of the eNodeB or gNodeB as well as the network manager provided by the same vendor. The gNodeB purpose-build elements are delivered with pre-installed vendor certificates signed by the vendor’s root of trust. Certificate management, including the certificate authority (CA) is typically handled by the network manager. The open interfaces in the O-RAN architecture enables a multi-vendor network with communication and management over standardized, open interfaces. To support certificate management, O-RAN has defined requirements using CMPv2 [6] covering the following use cases:
In 2026 WG11 will work with WG2, WG3, WG4, WG5, WG6 and WG10 to refine certificate management implementation details for each of these use cases.
Operator priorities will continue driving WG 11. Key 2026 initiatives in WG11 are to
[1] O-RAN Security Requirements and Controls Specifications, version 14.0, O-RAN ALLIANCE, February 2026.
[2] O-RAN Security Protocols Specifications, version 14.0, O-RAN ALLIANCE, February 2026.
[3] O-RAN Security Tests Specifications, version 12.0, O-RAN ALLIANCE, February 2026.
[4] O-RAN Security Threat Modeling and Risk Assessment, version 8.0, O-RAN ALLIANCE, February 2026.
[5] O-RAN Architecture Description, version 16, O-RAN ALLIANCE, February 2026.
[6] NIST Special Publication 800-207, "Zero Trust Architecture", August 2020, https://doi.org/10.6028/NIST.SP.800-207
[7] Zero Trust Maturity Model (ZTMM), version 2.0, US DHS CISA, April 2023.
by O-RAN ALLIANCE’s Security Work Group (WG11)